Why GKE Is the Most Advanced Managed Kubernetes Platform — A Technical Deep Dive
Audience: CTOs, CIOs, IT Architects, and Senior Engineering Leaders
Format: Evidence-based comparative analysis | APA 7th Edition references
Platforms compared: GKE · Azure AKS · AWS EKS · Oracle OKE · Cloud Run · Firebase
Executive Summary
Google Kubernetes Engine (GKE) is the most architecturally mature, operationally reliable, and feature-complete managed Kubernetes platform in the enterprise cloud market. This is not a vendor claim — it is a structural reality rooted in a foundational truth: Google invented Kubernetes.
The platform’s lineage traces directly to Google’s internal container orchestration systems, Borg and Omega, which managed billions of containers across Google’s global infrastructure for more than a decade before Kubernetes was open-sourced in 2014 (Burns et al., 2016).
This article delivers an evidence-based comparison of GKE against its primary managed Kubernetes competitors — Microsoft Azure AKS, AWS EKS, and Oracle OKE — across six critical dimensions. It also clarifies how GKE integrates strategically with Cloud Run and Firebase to form a comprehensive, unified cloud-native ecosystem.
1. The Origin of Kubernetes: Google’s Decade of Containerization
1.1 From Borg and Omega to Open Source
To fully appreciate GKE’s architectural advantages, you need to understand the engineering context from which Kubernetes emerged.
Google’s container orchestration journey began internally in the early 2000s with Borg — a large-scale cluster management system that managed hundreds of thousands of jobs across Google’s global data centers (Verma et al., 2015). Borg was not a prototype; it was the operational backbone powering Google Search, Gmail, and YouTube at planetary scale.
Following Borg, Google developed Omega — a more flexible, composable cluster management system that introduced optimistic concurrency control and a shared-state scheduler architecture (Schwarzkopf et al., 2013). Omega served as the intellectual bridge between Borg’s deterministic scheduling model and the declarative, extensible API model that would define Kubernetes.
In 2013, Google engineers — including Joe Beda, Brendan Burns, and Craig McLuckin — began designing Kubernetes as an open-source synthesis of the lessons learned from Borg and Omega. It was publicly announced in June 2014 and donated to the Cloud Native Computing Foundation (CNCF) in 2016 (CNCF, 2016; Google, 2014).
| |
1.2 Engineering Heritage as a Competitive Moat
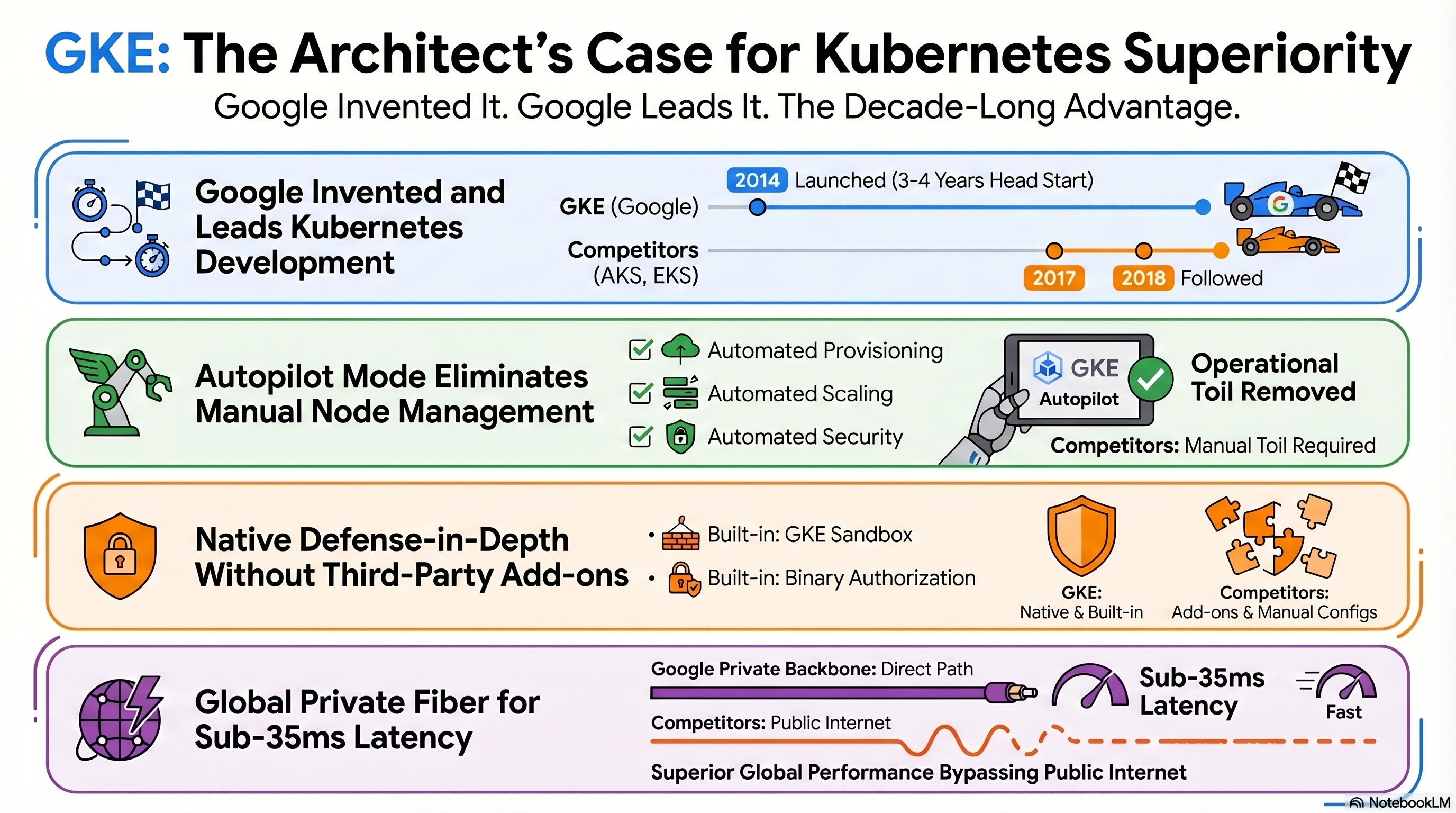
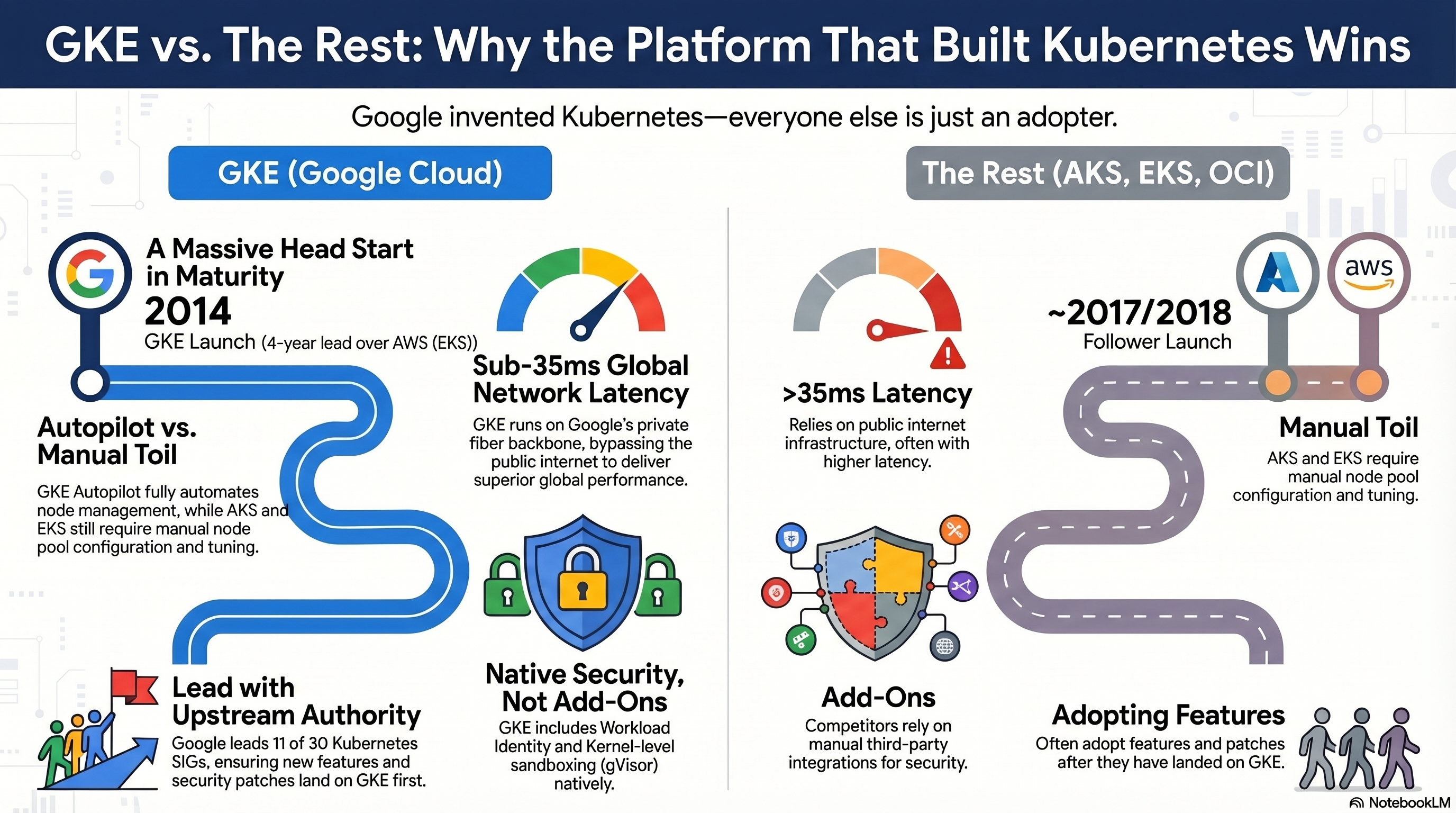
When Google launched GKE in 2014 — concurrent with Kubernetes’ public debut — the engineering team brought more than a decade of institutional knowledge in running containerized workloads at hyperscale.
| Platform | Launch Year | Head Start vs. GKE |
|---|---|---|
| GKE | 2014 | — |
| Azure AKS | 2017 | −3 years |
| AWS EKS | 2018 | −4 years |
| Oracle OKE | 2020 | −6 years |
This foundational advantage manifests concretely in GKE’s architecture: its control plane reliability, node auto-repair mechanisms, approach to workload identity, and autoscaling intelligence all reflect patterns proven over years of operating containers at Google scale. Competing platforms are fundamentally adopters of a framework that Google conceived, incubated, and continues to lead.
2. GKE vs. AKS vs. EKS vs. OKE: Comparative Analysis
Summary Table
| Dimension | GKE | AKS | EKS | OKE |
|---|---|---|---|---|
| Maturity | 10+ yrs Borg/Omega lineage; Autopilot mode; SRE-embedded automation | Launched 2017; strong Azure integration; manual node config required | Launched 2018; mature but relies on manual node group tuning | Launched 2020; primarily Oracle-workload focused |
| Autoscaling | HPA + VPA + Cluster Autoscaler; fully automatic in Autopilot | HPA/VPA available; Cluster Autoscaler functional; manual node pool config | HPA/VPA + Karpenter; complex configuration | Basic HPA/VPA; limited cluster-level intelligence |
| Security | Workload Identity, Binary Authorization, Shielded Nodes, GKE Sandbox (gVisor) — all native | Defender for Containers add-on; image signing via ACR | GuardDuty add-on; IAM Roles for Service Accounts | OCI IAM integration; limited sandbox options |
| Networking | Google private backbone (<35ms globally); Container-Native LB; Gateway API native | Azure CNI; regional load balancing; latency varies by region | VPC-CNI; ALB/NLB integration; region-constrained | OCI VCN; limited global network consistency |
| Control Plane SLA | 99.95%; zero-downtime upgrades with configurable disruption budgets | 99.95%; upgrade windows require explicit planning | 99.95%; control plane visibility limited | 99.95%; less documentation on upgrade automation |
| Upstream K8s | Leads 11 SIGs; features land in GKE first | Contributes to select SIGs; typically 1–2 releases behind | Growing contributions; historically conservative posture | Minimal upstream contributions |
Sources: Google (2023a); Microsoft (2023); AWS (2023); Oracle (2023); CNCF (2023)
2.1 Maturity and Operational Excellence
GKE’s Autopilot mode, introduced in 2021, represents a paradigm shift in managed Kubernetes operations. Unlike standard node-based provisioning models offered by AKS, EKS, and OKE, GKE Autopilot abstracts node management entirely — Google assumes full responsibility for node provisioning, configuration, scaling, security hardening, and bin-packing efficiency (Google, 2023a).
This is not merely a convenience feature. It is the culmination of Google’s SRE philosophy applied to Kubernetes cluster operations.
AKS and EKS both offer node pool management that reduces some overhead, but they fundamentally require platform teams to make decisions about instance types, disk configurations, and scaling policies. This operational surface area creates risk and demands sustained engineering investment. OKE, while capable, is primarily optimized for Oracle Cloud workloads and lacks the breadth of automation present in GKE (Oracle, 2023).
2.2 Scalability and Autoscaling Architecture
GKE implements a multi-dimensional autoscaling framework that simultaneously coordinates three mechanisms:
- HPA (Horizontal Pod Autoscaler) — pod-level scaling based on CPU, memory, or custom metrics
- VPA (Vertical Pod Autoscaler) — right-sizing resource requests and limits
- Cluster Autoscaler — node-level provisioning in response to pending pod scheduling pressure
In Autopilot mode, all three are managed automatically (Google, 2023b).
AWS EKS has partially addressed this gap through Karpenter — an open-source node provisioner offering faster scaling and more flexible instance selection (AWS, 2023). However, Karpenter requires explicit deployment and configuration by platform teams, whereas GKE’s equivalent is native and policy-enforced. AKS offers functional autoscaling but lacks the tight integration between its node and pod scaling layers that GKE’s control plane provides natively.
2.3 Security Architecture
GKE’s security model is distinguished by the depth and nativity of its controls:
| Control | GKE | AKS | EKS | OKE |
|---|---|---|---|---|
| Pod Identity (no static credentials) | ✅ Workload Identity (native) | ⚠️ Managed Identity (add-on) | ⚠️ IRSA (manual config) | ⚠️ OCI IAM (manual config) |
| Image attestation at deploy time | ✅ Binary Authorization (native) | ⚠️ Azure Policy (add-on) | ⚠️ ECR signing (optional) | ❌ Limited |
| Trusted boot / verified firmware | ✅ Shielded GKE Nodes (native) | ⚠️ Trusted Launch (optional) | ❌ Not available | ❌ Not available |
| Kernel-level sandbox | ✅ GKE Sandbox / gVisor (native) | ❌ Not available natively | ❌ Not available natively | ❌ Not available |
Workload Identity provides cryptographically verifiable pod identities mapped to Google Cloud IAM service accounts, eliminating static credential mounting — a common vulnerability vector in competing platforms (Google, 2023c).
Binary Authorization enforces a deploy-time policy requiring container images to be attested and signed by trusted authorities before scheduling, providing supply chain security at the control plane level.
GKE Sandbox, powered by gVisor, introduces an additional isolation layer between container workloads and the host kernel — a capability with no native equivalent in AKS, EKS, or OKE (Google, 2020).
2.4 Networking and Global Reliability
GKE benefits from Google’s private global fiber network — the same infrastructure that powers Google Search, YouTube, and Google Workspace — offering sub-35ms latency between major metropolitan regions worldwide (Google, 2023d). This is not shared public internet routing; Google’s backbone carries traffic over dedicated interconnects between Points of Presence (PoPs).
Key networking differentiators:
- Container-Native Load Balancing routes traffic directly to pod IP addresses, bypassing node-level proxy hops, reducing latency and improving distribution accuracy
- Gateway API is natively supported with advanced traffic management (header-based routing, traffic weighting, cross-namespace policies) — requiring manual third-party ingress controllers in AKS/EKS
- Anycast routing ensures global traffic is served from the nearest healthy endpoint without manual DNS or failover configuration
2.5 Automation and Operational Simplicity
GKE Autopilot enforces Pod Security Standards by default — including restrictions on host networking, privileged containers, and host path mounts — that must be manually configured in competitor platforms.
Automated node upgrades use a surge upgrade strategy that maintains cluster capacity during the upgrade cycle, with configurable disruption budgets that respect PodDisruptionPolicies (Google, 2023a).
AKS and EKS offer maintenance windows for upgrades but require explicit enrollment and configuration. Node drain and cordon operations during upgrades are not as transparently automated, and organizations frequently encounter upgrade-related disruptions in production when manual node group configurations are suboptimal (Microsoft, 2023; AWS, 2023).
2.6 Ecosystem Leadership and Upstream Kubernetes Alignment
Google’s contribution to the upstream Kubernetes project is unmatched among cloud providers.
As of 2023, Googlers lead or co-lead 11 of the 30 active Kubernetes SIGs — including the critical SIG-Architecture, SIG-Node, and SIG-Network working groups that define the platform’s core primitives (CNCF, 2023).
This leadership translates into a measurable first-mover advantage: features that enter alpha or beta in upstream Kubernetes typically become available in GKE before AKS or EKS implement them. Notable examples:
- Native Kubernetes Gateway API integration
- Early support for Ephemeral Containers for live debugging
- Adoption of Structured Logging prior to competitor implementations
Microsoft has increased upstream contributions, primarily through Cluster API (CAPI) and Windows node support. AWS has historically maintained a more conservative upstream posture, prioritizing stability over feature velocity (CNCF, 2023).
3. GKE, Cloud Run, and Firebase: A Unified Cloud-Native Ecosystem
Google Cloud’s managed compute portfolio is designed around a principle of progressive abstraction: choose the level of control appropriate to your workload requirements.
Platform Selection Framework
| Decision Criterion | GKE | Cloud Run | Firebase |
|---|---|---|---|
| Use case complexity | Complex microservices, stateful workloads, multi-tenant | Stateless services, event-driven, APIs | Mobile/web apps, real-time data, auth |
| Operational model | Full K8s control (or Autopilot) | Fully managed, no cluster management | Fully managed, no-ops backend |
| Scaling model | HPA + VPA + Cluster Autoscaler | Scale to zero, automatic | Firebase-managed, automatic |
| Hybrid/Multi-Cloud | ✅ Yes — via Anthos/Fleet | ⚠️ Limited (Cloud Run for Anthos) | ❌ No |
| State management | Stateful with PersistentVolumes | Stateless only | Firestore (document DB) |
| Primary audience | Platform/SRE teams, enterprise architects | Backend developers, DevOps | Frontend/mobile developers |
| Kubernetes required | ✅ Yes | ❌ No (Knative-based) | ❌ No |
Sources: Google (2023a, 2023e, 2023f)
3.1 GKE — Full Orchestration Control
GKE is the appropriate choice for organizations managing:
- Complex microservices architectures
- Stateful distributed systems
- Hybrid cloud deployments
- Workloads requiring fine-grained control over scheduling, networking, and security policies
It supports the full Kubernetes API, including CRDs, Admission Webhooks, and the complete ecosystem of CNCF-graduated tooling — Prometheus, Argo CD, Istio, Crossplane, and more.
GKE integrates with Anthos — Google’s multi-cloud and hybrid management platform — enabling consistent policy enforcement, workload management, and configuration synchronization across on-premises infrastructure and competing cloud providers (Google, 2022). This positions GKE as the strategic control plane for enterprises pursuing cloud-agnostic or multi-cloud architecture.
3.2 Cloud Run — Serverless Container Simplicity
Cloud Run is Google’s fully managed serverless container platform, built on Knative — the open-source framework that Google co-developed with IBM and SAP (Google, 2023e).
Designed for developers who require container portability without cluster management overhead, Cloud Run:
- Automatically provisions infrastructure
- Scales to zero when idle; scales horizontally on traffic spikes
- Uses a per-request billing model that eliminates idle compute costs
It is ideally suited for:
- Stateless HTTP services
- Event-driven processing triggered by Pub/Sub or Cloud Scheduler
- API backends requiring rapid iteration cycles
Cloud Run for Anthos enables serverless workloads to execute within existing GKE clusters, sharing network policies, service mesh, and node infrastructure — a hybrid model that preserves operational consistency while offering developer-friendly deployment abstractions (Google, 2023e).
3.3 Firebase — Serverless Backend for Frontend Applications
Firebase is Google’s application development platform optimized for mobile and web frontends requiring real-time data synchronization, user authentication, serverless function execution, and static site hosting (Google, 2023f).
Its constituent services — Firestore, Firebase Authentication, Cloud Functions for Firebase, Firebase Hosting, and Firebase App Distribution — are integrated through a cohesive SDK that significantly reduces time-to-market for consumer-facing applications.
Important: Firebase is not a containerized or Kubernetes-adjacent platform. It is a backend-as-a-service (BaaS) targeted at application developers, not infrastructure engineers. It is not appropriate for complex microservices, containerized workloads, or enterprise systems requiring granular infrastructure control.
3.4 Decision Summary
| |
4. Strategic Conclusion: Why Leading Organizations Choose GKE
The convergence of foundational heritage, engineering leadership, operational automation, and ecosystem depth places GKE in a category of its own. The strategic rationale distills into five pillars:
4.1 Inventorship and Architectural Authority
Google invented Kubernetes and continues to drive its architectural evolution through sustained leadership of the CNCF’s SIG structure. This inventorship translates into a measurable technical advantage: GKE receives new Kubernetes capabilities earlier, with higher upstream alignment and lower deviation from the Kubernetes API specification than any competing managed platform (CNCF, 2023; Burns et al., 2016).
For organizations investing in Kubernetes as a long-term infrastructure foundation, alignment with the platform’s inventor reduces future migration risk and maximizes the value of engineering skills investments.
4.2 Automation That Eliminates Operational Toil
GKE Autopilot’s fully managed node lifecycle — encompassing provisioning, auto-repair, bin-packing optimization, and policy enforcement — directly reduces the operational toil that consumes platform engineering capacity in AKS and EKS environments.
Google’s SRE literature defines toil as “manual, repetitive, tactical work with no enduring value” (Beyer et al., 2016). GKE’s automation model operationalizes SRE principles at the platform level, allowing platform teams to redirect capacity from cluster maintenance toward value-generating application delivery.
4.3 Security Depth Without Third-Party Dependency
GKE’s native security architecture — Workload Identity, Binary Authorization, Shielded Nodes, and GKE Sandbox — provides a defense-in-depth posture that does not depend on optional add-on services or third-party integrations (Google, 2023c).
This reduces the security operations surface, simplifies compliance attestation, and ensures that security controls are enforced uniformly across all workloads by the platform itself. For regulated industries — financial services, healthcare, government — this native security posture is a significant risk reduction factor.
4.4 Global Network Performance as Infrastructure
The performance advantages conferred by Google’s private global network are not configurable options or premium service tiers — they are structural properties of GKE’s networking architecture. Container-Native Load Balancing, global Anycast routing, and low-latency interconnects between Google’s PoPs are inherent characteristics of any GKE deployment (Google, 2023d).
For globally distributed applications with latency-sensitive transactional workloads, this network architecture represents a durable competitive advantage over regionally constrained alternatives.
4.5 Ecosystem Coherence Across Compute Abstractions
GKE’s integration with Cloud Run and Firebase within the Google Cloud ecosystem enables organizations to adopt the right compute abstraction for each workload type without fragmenting their operational tooling, identity model, network security posture, or observability stack.
Google Cloud’s unified IAM model, Cloud Monitoring, Cloud Logging, and Security Command Center apply consistently across GKE, Cloud Run, and Firebase deployments — a level of ecosystem coherence that is difficult to achieve when mixing managed Kubernetes from one vendor with serverless from another (Google, 2023a, 2023e, 2023f).
Final Verdict
GKE is not simply a Kubernetes service — it is the platform that Kubernetes was built to become.
| Advantage | GKE Lead |
|---|---|
| Kubernetes origin & SIG leadership | Structural — not replicable |
| Autopilot / zero node management | 3–4 year design advantage |
| Native security stack | No equivalent in AKS/EKS/OKE |
| Google private network backbone | Infrastructure-level, not configurable |
| Ecosystem (GKE + Cloud Run + Firebase) | Unified IAM, logging, observability |
For enterprise leaders evaluating managed Kubernetes platforms, the evidence is clear: GKE reduces operational overhead, accelerates modernization initiatives, and provides the most defensible long-term foundation for cloud-native architecture.
Youtube
References
Amazon Web Services. (2018). Amazon Elastic Kubernetes Service (EKS). https://aws.amazon.com/eks/
Amazon Web Services. (2023). Amazon EKS documentation. https://docs.aws.amazon.com/eks/
Beyer, B., Jones, C., Petoff, J., & Murphy, N. R. (2016). Site reliability engineering: How Google runs production systems. O’Reilly Media.
Burns, B., Grant, B., Oppenheimer, D., Brewer, E., & Wilkes, J. (2016). Borg, Omega, and Kubernetes. ACM Queue, 14(1), 70–93. https://doi.org/10.1145/2898442.2898444
Cloud Native Computing Foundation. (2016). CNCF charter. https://github.com/cncf/foundation/blob/main/charter.md
Cloud Native Computing Foundation. (2023). Kubernetes contributor statistics. https://k8s.devstats.cncf.io/
Google. (2014). Google open sources Kubernetes. https://opensource.googleblog.com/2014/06/an-update-on-container-support-on-google-cloud-platform.html
Google. (2020). GKE sandbox with gVisor. https://cloud.google.com/kubernetes-engine/docs/concepts/sandbox-pods
Google. (2022). Anthos overview. https://cloud.google.com/anthos/docs/concepts/overview
Google. (2023a). GKE Autopilot overview. https://cloud.google.com/kubernetes-engine/docs/concepts/autopilot-overview
Google. (2023b). Cluster autoscaler and VPA in GKE. https://cloud.google.com/kubernetes-engine/docs/concepts/cluster-autoscaler
Google. (2023c). GKE security overview. https://cloud.google.com/kubernetes-engine/docs/concepts/security-overview
Google. (2023d). GKE networking overview. https://cloud.google.com/kubernetes-engine/docs/concepts/network-overview
Google. (2023e). Cloud Run documentation. https://cloud.google.com/run/docs
Google. (2023f). Firebase documentation. https://firebase.google.com/docs
Microsoft Azure. (2017). Azure Kubernetes Service (AKS). https://azure.microsoft.com/en-us/products/kubernetes-service
Microsoft. (2023). AKS documentation. https://learn.microsoft.com/en-us/azure/aks/
Oracle. (2023). Oracle Container Engine for Kubernetes (OKE) documentation. https://docs.oracle.com/en-us/iaas/Content/ContEng/home.htm
Schwarzkopf, M., Konwinski, A., Abd-El-Malek, M., & Wilkes, J. (2013). Omega: Flexible, scalable schedulers for large compute clusters. Proceedings of the 8th ACM European Conference on Computer Systems (EuroSys ‘13), 351–364. https://doi.org/10.1145/2465351.2465386
Verma, A., Pedrosa, L., Korupolu, M., Oppenheimer, D., Tune, E., & Wilkes, J. (2015). Large-scale cluster management at Google with Borg. Proceedings of the Tenth European Conference on Computer Systems (EuroSys ‘15). https://doi.org/10.1145/2741948.2741964
Published under technical editorial review. All architectural claims reference official vendor documentation and peer-reviewed academic sources per APA 7th Edition.